The Operations Technology (OT) vs. Information Technology (IT) Debate Turns to Better Security
Best practices like network segmentation, encryption and visibility into operations technology-level communications matter to today’s warehouse operators. While they need better uptime, they also must assure IT that sound security methods will be followed.

In this age of Internet of Things (IoT), connectivity, and the time pressures of e-commerce fulfillment, one killer IoT app would seem to be remote monitoring of automated materials handling equipment. Get more equipment analyzed using the IoT and distribution center operators and their equipment providers should be able to squeeze more uptime from the assets.
But the one sticking point to this value proposition is data security. The operations technology (OT) managers in a company may see the benefits of IoT-enabled asset monitoring, but the information technology (IT) leadership may see IoT connectivity as a security threat.
Materials handling solution vendors as well as providers that specialize in industrial connectivity say these security concerns and OT/IT tensions are real, but can be overcome. Better cooperation around system architecture and more effort to show IT leaders that best practice security measures will be used should go a long way to easing concerns.
Done right, IoT-connected machinery offers uptime rewards at minimal risk. But, by the same token, when it’s done wrong, that connectivity into OT systems can pose big threats. “For sure, connectivity is a double-edged sword,” says Keith Blodorn, director of program management at ProSoft Technology, which specializes in industrial communications and remote access solutions. “Integrating these systems can provide a lot of efficiency and help with goals like uptime, but at the same time, as things become more connected, they become more vulnerable.”
Some DCs have run up against hurdles when trying to set up remote monitoring of materials handling equipment due to data security policies, confirms Ken Johnson, vice president of sales and customer service at Dematic, an automated materials handling provider. This reluctance is understandable, given the steady stream of news about hacking incidents, he adds.
“There are so many data security risks today, that if they can’t solve those security issues with remote monitoring, it’s hard to blame IT for not letting the connections happen,” Johnson says. “But somehow, we have to solve these security issues. On the operations side, the concern is that there needs to be some means of remote support by the [automation equipment] vendor, because the user company can’t always wait for the vendor to fly in a technician to fix things.”
Operationally, e-commerce fulfillment has made maximum uptime for materials handling systems imperative. When the cycle time for processing orders can be just a few hours, the days of waiting a day or two for a repair are no longer acceptable, says Johnson. “Given the order fulfillment processing times we have in some facilities, it’s all about increased uptime on the operations side,” says Johnson. “But the security issues are huge. We have to find a way to balance these priorities.”
Connected but secure
In the past, automated equipment and control systems ran on closed, proprietary networks. There was less chance of equipment or programmable logic controllers (PLCs) getting hacked, because they weren’t directly connected to enterprise networks or the Internet. 
But now, OT-level systems are more open. Specialized fieldbus networks have given way to more open Ethernet-based industrial networks that can more easily exchange data with enterprise networks and systems. Wireless networks and IoT connectivity further opens what were once closed-off OT systems to potential threats. The fear is not only that OT systems could be tampered with, but that a breach could happen to enterprise-level data by hackers gaining entrance from a connection at the OT level.
“You can’t just start connecting equipment all over the place without thinking through the risks and putting in place appropriate measures,” says Johnson. “So now I think companies are stepping back and saying, because of security risks, we don’t need everything on one big network. We have to separate the [OT and IT] networks somehow, and put in place the proper security.”
The main way to avoid security vulnerabilities while enabling connectivity to assets, says Blodorn, is to provide multiple layers of defense. This includes technology such as firewalls to segment OT networks from IT networks, and within remote connectivity solutions, use of technology such as HTTP-Secure, better known as HTTPS, and virtual private networks (VPNs) that support authentication and encryption of the data flowing from the OT level to the enterprise level. “[With VPNs and HTTPS] everything can be encrypted and in effect, moving in its own secure little tunnel,” says Blodorn.
Companies looking to connect to OT systems can study recommended practices put forth by organizations such as the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT), a project under a division of the U.S. Department of Homeland Security, says Blodorn. ISA’s ISA/IEC 62443 series of industrial automation and control systems (IACS) security documents are another source of best practices, as well as guidance put forth by PLC and automation vendors such as Rockwell Automation, Blodorn adds.
Common recommendations include making use of firewalls and gateways to create secure boundaries between OT and IT systems, which offers a “demilitarized zone,” or DMZ, between the OT and IT realms. Overall, says Blodorn, the best practice is not any single mechanism, but rather a “defense in depth” strategy that poses multiple barriers.
“Defense in depth is all about putting in place multiple defense mechanisms, each of which takes a different skill to defeat,” says Blodorn. “It’s also more procedural than technical in that you have to look at your network and understand how people interact with it. Then, you make sure that you are leaving in place only the secure access and connectivity you want, and nothing else.”
While firewalls have their use, some industrial network security experts say that an OT/IT software gateway that can parse and understand the nature of requests is needed. Francis Cianfrocca, founder and chief security officer with Bayshore Networks, a provider of an OT/IT gateway solution, says firewalls work at isolating networks from each other, but can’t examine the commands moving between the OT to IT level to see if something unusual is being triggered.
“What we do is put in a platform that looks like a firewall that sits on that boundary between the OT network and the IT network, and look at all the data coming through. But rather than filtering it by IP addresses and ports like a firewall, it filters it by data,” says Cianfrocca. “We can look at a set of commands coming in, and if it’s a command that asks for something normal like ‘tell me the speed of this conveyor’ or other industrial parameters, that’s fine, we let those through. But if we see an unusual request, like, ‘let’s change the position of this robot,’ or ‘stop this conveyor’—that type of request we can block.”
Cianfrocca calls this functionality “granular content inspection,” and says it’s needed to arrive at a “content aware” defense between OT and IT layers to make it possible to enforce security policies. “We can develop and enforce policies that are going to protect your systems, even while allowing remote connectivity to an equipment vendor, or to feed data to the enterprise level for analysis,” he says.
Finding a balance
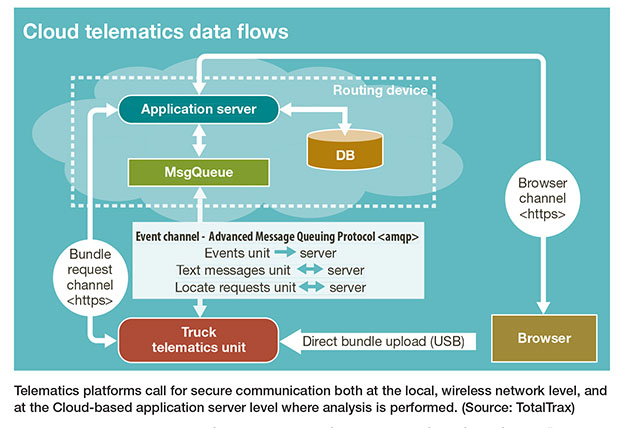
Real-time tracking solutions for warehouse assets such as lift trucks generate a wealth of data about driver behavior, and vehicle and inventory movement that can be used to enhance productivity and safety, but it means more data flowing wirelessly in a warehouse, and then to the Cloud for analysis. As a result, IT departments are often concerned that the proper wireless security protocols and Cloud application security measures are in place, says Frank Cavallaro, CEO of TotalTrax, a provider of real-time tracking and fleet management solutions.
“Our prospects and customers are definitely concerned about security,” says Cavallaro. “It runs the gambit from companies who are committed to the Cloud and tell us the protocols they want us to conform to, while at the other end of the spectrum, we have companies who want us to show them the way.”
To provide secure local wireless traffic, TotalTrax supports established wireless network security protocols such as WPA, WPA 2, and Protected Extensible Authentication Protocol (PEAP), says Cavarallo. “When we show how our platform supports these protocols, and we demonstrate our knowledge of them through our tech services people, the IT folks warm right up to that,” says Cavarallo.
Similarly, enterprise IT groups want to know proper security measures are in place for Cloud-based analysis of telematics data. At this level of security, partnering for Cloud infrastructure with “brand name” providers such as RackSpace, Microsoft or Amazon alleviates IT concerns because they know these providers are experts in Cloud security. “If you say you are using one of these brand names for Cloud infrastructure, you get a nod of approval from IT,” says Cavarallo.

ProSoft’s Blodorn agrees that a vendor’s ability to assure IT managers that solutions follow a secure architecture is a big part of the answer to security hurdles. “We have information about our products and services available to our customers that speaks to the IT side of the things on data security—the mechanisms we are using,” says Blodorn. “It gives OT and IT people more tools to decide whether or not to allow a connection.”
Blodorn also recommends that OT and IT managers sit down together to discuss secure architecture for industrial control systems, as well as the business benefit of having remote diagnostics. “Hopefully the conversion gets to the point where there is the recognition that we need to be able to provide service organizations with remote access to equipment to better maintain it and improve uptime,” he says. “And once there is that recognition of the value involved in connectivity, you can examine how to achieve it in a way that segregates and secures network functions, and doesn’t open up vulnerabilities.”
Besides security mechanisms such as encryption, there are various deployment options for remote connectivity to automation. One alternative for remote monitoring, notes Blodorn, is to use an industrial cellular gateway to connect into PLCs and move data using a carrier’s cellular network, rather than up through the user organization’s enterprise network and Internet connection.
Another alternative for companies wanting some benefits of remote diagnostics but don’t want to permit an IoT type of connection is the leverage some “view only” tools, says Johnson. Along these lines, Dematic has introduced a smart phone app that allows someone in a warehouse to show a Dematic tech support operator a camera view of PLC lights or other visual indicators to diagnose a problem remotely.
The tool—called Dematic SiteView—is view only, says Johnson, so there is zero danger of someone hacking into systems. “Sometimes if our expert is just able to see the lights on a PLC, they can quickly diagnose a problem,” says Johnson. “It’s a bit of a Band Aid [to full remote monitoring], but when you can’t log in, at least we’re able to see what is going on.”
John Sorensen, senior vice president and general manager of lifecycle support services for Intelligrated, an automated materials handling systems provider, says Intelligrated has helped some users with secure remote monitoring of their systems, using a team approach that brings IT managers into the discussion early on.
“From my experience, it needs to be a partnership, involving the people in the user organization—both from operations and IT—as well as the system supplier and support organization to make sure the right solution is put in place that is bulletproof and achieves the operational goals.”
Some organizations that don’t want to allow remote connectivity to a control network or the controls for an automated system may sometimes be fine with a remote connection to a local data historian or database that stores data generated by the equipment, says Sorensen. That makes the connectivity once removed from the controls layer, but permits remote access to data that be analyzed for trends that impact uptime. As Sorensen sums things up, “it takes a balancing act and a team approach to figure out the right connectivity options to maximize both security and the benefits of real time monitoring.”
Companies mentioned in this article:

Article Topics
MRO News & Resources
Avidbots showcases autonomous cleaning robots Traka exhibits modular lockers MRO Survey: Finding and keeping the best technicians Maintenance, Repair and Operations: Understanding the true condition of the equipment Newly formed Bison combines AMETEK DFS and Bison Gear and Engineering Corp. Building (and maintaining) your maintenance, repair and operations (MRO) tech workforce The power side of lift truck battery and charger maintenance More MROLatest in Materials Handling
Automate & Accelerate: Replacing Pick-to-Light with the Next Generation of Automation 6 Ways to Re-evalute Fulfillment This Year MHEFI awards record-breaking $231,700 in scholarships to 61 students ALAN opens nominations for 2024 Humanitarian Logistics Awards Kenco to install an AutoStore system at its Jeffersonville, Ind., DC Schneider Electric rolling out WMS and TMS solutions from Manhattan Associates at scale Leaders Q & A with Bryan Ferguson: Resurgence of RFID technology More Materials HandlingAbout the Author
Subscribe to Materials Handling Magazine

Find out what the world's most innovative companies are doing to improve productivity in their plants and distribution centers.
Start your FREE subscription today.
May 2024 Modern Materials Handling

Latest Resources










